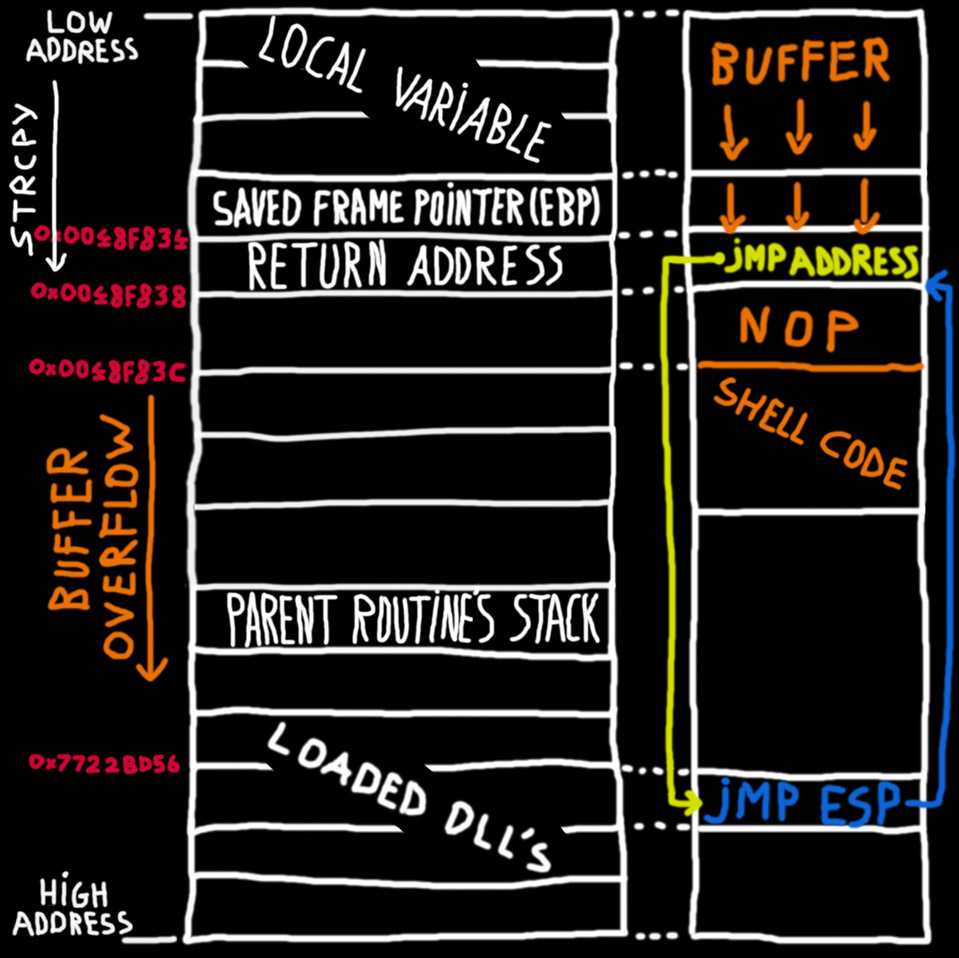
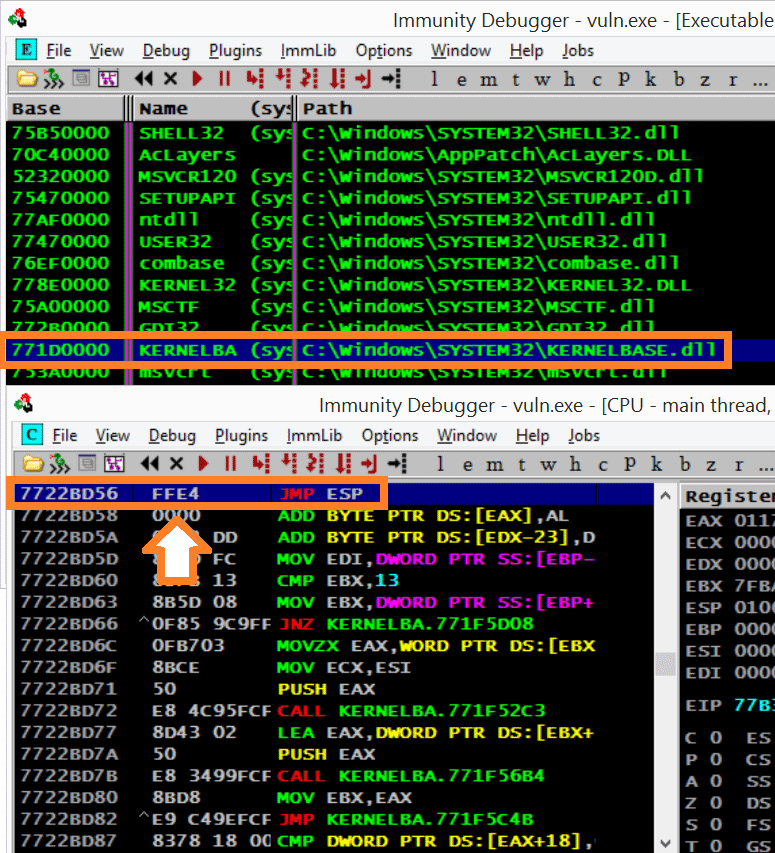
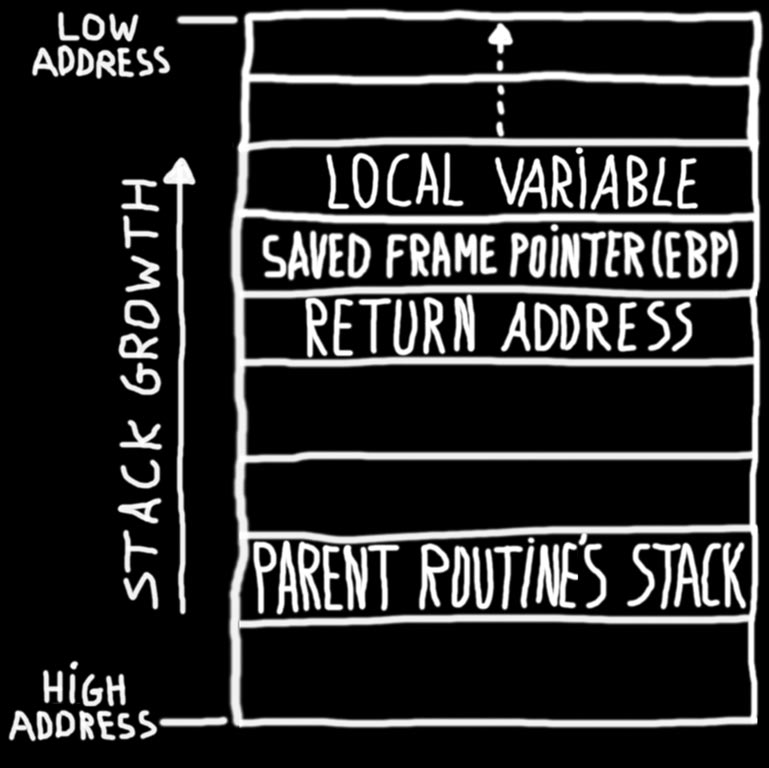
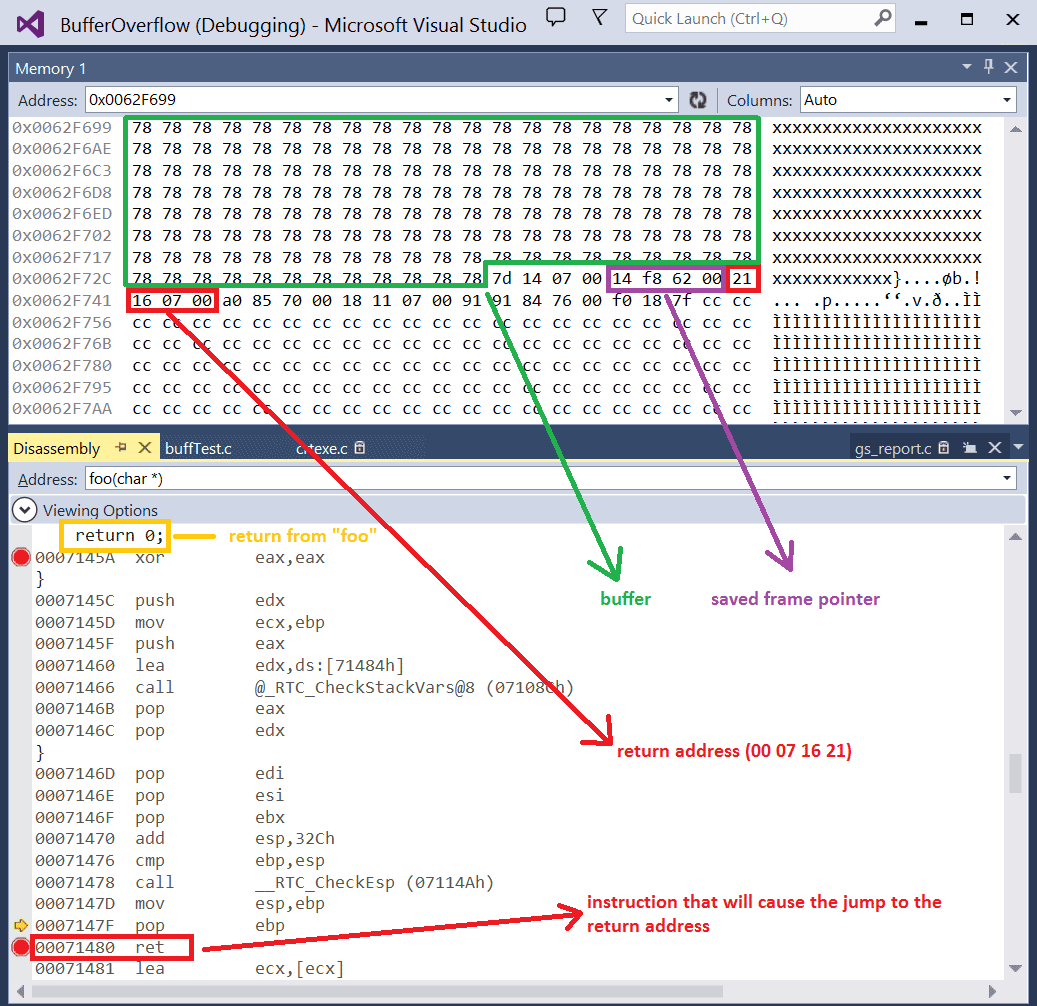
Lab 3 report.docx - Ankit Kumar 773312668 Buffer Overflow Vulnerability Lab Report Task 1: Non-root stack program Debug stack Figure 1.1 Return address | Course Hero

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily on a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero

swift - HKWorkoutRouteBuilder and CLLocationManager only adding route updates in increments - Stack Overflow
Buffer Overflow Network Security Computer Network Attack, PNG, 1240x1346px, Buffer Overflow, Area, Attack, Computer Network, Computer

LAB1.pdf - 601.443/643 – Buffer Overflow Vulnerability Lab 1 Part 1: Buffer Overflow Vulnerability Lab Copyright © 2006 - 2016 Wenliang Du, Syracuse | Course Hero